One of the most common questions I get on the first call with a prospective Fig customer is some version of "but we are only five people - do we really need to do DCC properly?". The answer is yes. The MOD's Cyber Risk Profile is driven by the contract, not the supplier's headcount. A three-person consultancy holding a Very Low CRP contract faces the same L0 evidence requirements as a 150-person supplier on the same contract profile.
The good news is that L0 is proportionate for genuinely small organisations. The five technical controls can be evidenced in a day or two by a competent IT lead, and the governance documentation is not as heavy as the scheme's marketing material suggests. What catches small suppliers out is a different set of things: scope, governance, and the habit of keeping evidence that would survive an auditor's eye.
Why small does not mean exempt
DCC is contractual. Your MOD buyer specifies a Cyber Risk Profile for the contract, and the scheme maps that CRP to a required DCC level. The supplier holds the certificate for the contract-in-scope, not for the business as a whole.
That distinction matters for small organisations. A three-person firm holding one Very Low CRP contract needs L0 for that contract. A three-person firm holding one Low CRP contract needs L1. The supplier size does not change the certification requirement.
What does change for smaller suppliers is proportionality of evidence. Assessors do not expect a five-person consultancy to have an enterprise ISMS. They do expect:
- A written Information Security Policy that actually reflects how the business operates.
- An Incident Response Plan that names real people, not role titles that do not exist at that organisation.
- Evidence that the five technical controls are operational, from real tooling - not "we use Windows Defender" on its own.
The evidence volume is lower. The rigour is the same.
What DCC Level 0 looks like for a 1-9 person supplier
For a typical micro organisation the L0 evidence pack has these components:
Cyber Essentials certificate (current). Non-negotiable prerequisite. If you do not hold one, Fig can bundle CE with DCC as a single engagement.
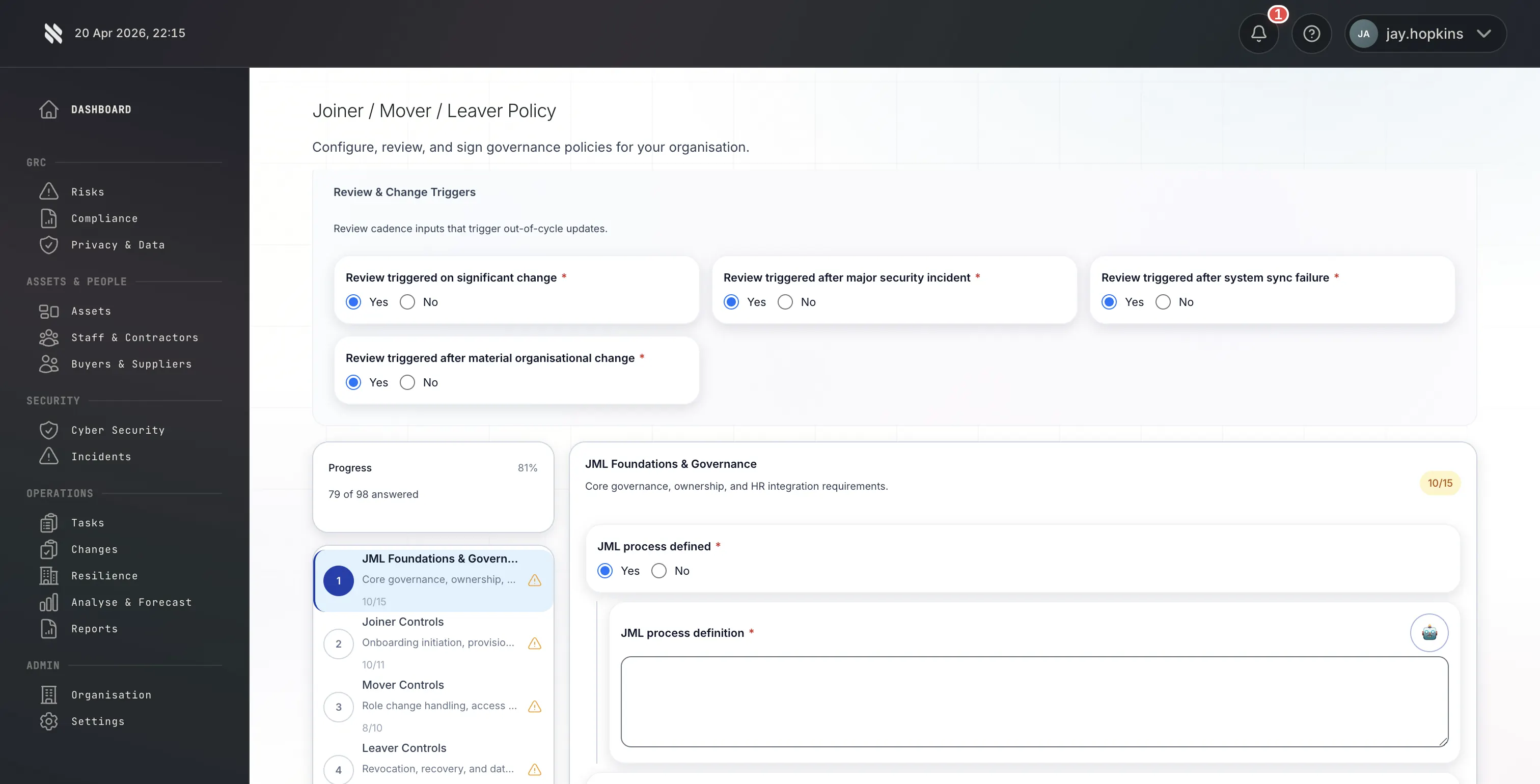
Information Security Policy (4-8 pages). Coverage: acceptable use, data classification, incident reporting, joiner-mover-leaver, remote working, supplier due diligence. For a small business this can be a single document, reviewed annually, signed by a director.
Incident Response Plan (2-3 pages). Named responders, notification thresholds, MOD contact route, recovery procedures. In a small firm this is usually one or two people taking the "incident response lead" role, with a clear escalation path to a named director.
Technical control evidence. Firewall rulesets for the office and home workers, MDM or equivalent endpoint management evidence, patch reports for at least the last 30 days, MFA configuration for Microsoft 365 / Google Workspace / cloud admin accounts, AV/EDR coverage evidence, user access control records.
Supply chain evidence. Even small firms have suppliers. A short document listing your own critical suppliers (hosting, SaaS, outsourced services), what they do for you, and the security assurance you hold over them.
Staff vetting evidence. Pre-employment checks for anyone handling MOD information. For genuinely small firms this is often a statement that the directors and employees have been screened, with employment and identity checks on file.
See the full DCC requirements checklist for the consolidated L0 + L1 readiness list.
Where small suppliers actually trip up
Over dozens of engagements, a consistent pattern emerges. Small suppliers rarely fail L0 on technical controls. They fail on governance and scope:
Scope. Small firms often have blurred boundaries between personal and business IT. The founder's laptop is also the family laptop. Subcontractors work with the supplier's data on their own machines. BYOD is treated as a non-issue. The assessor will challenge each of these; small suppliers need to draw clear boundaries around what is in scope and apply the same controls within that boundary. Our DCC L0 scoping guide covers the common traps.
Governance documentation. The instinct in a small business is to treat the Information Security Policy as a box-tick. Assessors read policies. They check whether the policy matches observable practice. A policy saying "we review access quarterly" and zero evidence of a review happening will produce a finding.
Evidence quality. Small firms often have the right controls in place but no record of them. "We patch every week" without a patch dashboard export, or "we review access when people leave" without a leaver's log, will prompt clarification requests.
Subcontractor relationships. A small consultancy that passes work to two associates under a labour contract has a supply chain even though it does not feel like one. The assessor will ask how you assure those associates handle MOD data appropriately.
What Fig's L0 engagement looks like for a micro organisation
For 1-9 employees Fig's L0 price is £999.99 + VAT. That covers:
- CSM v4 Level 0 assessment by an IASME-licensed Fig Group assessor.
- Governance and supply chain evidence review.
- Up to three rounds of assessor feedback included in the fee.
- Certificate issuance and three-year validity with annual attestation.
- IASME DCC register listing.
Cyber Essentials is a prerequisite and is priced separately, though we can bundle it on request.
We deliver L0 for small organisations quickly because the evidence volume is proportionate. A prepared micro organisation completes L0 in 2-3 weeks end-to-end; one starting from a lower baseline takes 4-6 weeks.
Planning ahead: when to think about L1
If you expect your MOD pipeline to include Low CRP contracts, now is the time to plan the L0 → L1 progression. L1 is a more substantial engagement (see the DCC L1 preparation guide), and the governance foundation built for L0 accelerates L1 preparation later.
Micro suppliers that plan to stay L0-only can run the annual attestation cycle lightly. Micro suppliers expecting L1 in the next 6-12 months should use the L0 engagement to stand up the broader governance artefacts L1 will need anyway - risk register, business continuity plan, basic ISMS structure.
The practical next step
If you are a small business preparing for DCC L0, the cheapest insurance is a scoping conversation before you start assembling evidence. A 30-minute call with Fig typically saves a small supplier a week of wasted preparation on scope questions the assessor would eventually reject.
Talk to a DCC expert → | See L0 micro pricing →